This document provides information on a range of topics that may need to be reviewed by stakeholders as part of the process of purchasing a Gorilla subscription or getting approval from your Internal Review Board or Ethics Committee. If you have further questions, please don't hesitate to contact us by email (info@gorilla.sc).
If you want to read more about Gorilla Product and its Technical Side visit our Gorilla FAQ page.
Gorilla is made, owned and sold by Cauldron Science Ltd (Cauldron).
Cauldron is incorporated in England and Wales under company number 07071678. Our VAT number is GB996693829. We are a micro-SME.
We are registered with the ICO under registration number ZA245277.
Our registered office is: 2 Old Bath Road, Newbury, Berks, RG14 1QL
Our business address is: St John's Innovation Centre, Cowley Road, Cambridge, CB4 0WS.
Please find below, links to our Terms and Conditions documentation:
Gorilla is hosted on Microsoft Azure within the EU (Republic of Ireland) which is compliant with ISO/IEC 27001:2005. Our backups are located in the Netherlands.
We also use a range of other suppliers. We have a signed Data Processing Agreement (DPA) with each of them, and we ensure that all of our providers have excellent security and privacy in place and are fully GDPR compliant.
We use a limited subset of suppliers to process participant data.
We also have a full list of the suppliers we use to process researcher/user data.
You are the owner (Data Controller) of any data you collect (participant data from any experiment where your account is the project owner). We will never view or use your participant data, unless we receive your explicit permission (i.e. if you have a support question about your data).
Your data is downloadable from your experiment as a spreadsheet, and once you download it you have complete control over how it is stored and used.
You can choose to delete participant data you own (participant data from any experiment where your account is the project owner) at any time.
You can also choose to delete your account at any time. You can find steps to delete your Gorilla account in our Gorilla FAQ guide.
Deleted data is cleared from our backups within 14 days.
You cannot delete data or accounts from other users, even if you are their subscription manager or university supervisor. Accounts are owned by the individual user, not by the university or company. You can remove a user from your subscription and reclaim their unused participant tokens, see our subscription administrators guide for more information.
Cauldron Science Ltd understands the importance of ensuring that its product is usable by all, including people with disabilities.
For a closer look, view our accessibility roadmap.
We're often asked to provide draft text for an Internal Review Board (IRB) or Ethics Committee. Below you will find information about Gorilla that could be useful for your application.
We will use Gorilla (www.gorilla.sc) to collect data for our study. Gorilla is a cloud software platform specifically for the behavioural sciences. Here are some key facts about their data security:
In compliance with BPS (The British Psychological Society) requirements, identifying data, demographic information and performance data are all stored separately. They are downloaded separately from the Data tab and joined together outside Gorilla using the Private IDs provided.
Our database architecture supports double-blind studies; you can join demographic data with performance data while remaining blinded.
Participant Data collected using Gorilla is anonymous by default. The only exceptions to this are (1) when using email based recruitment policies as Gorilla requires the participants email address to send them emails, (2) experiments in which the researcher elects to use personally identifying participant IDs and (3) the researcher collects personally identifying data as part of their study. In all cases, the participant would have given their consent.
Data files from Gorilla provide a Public and Private participant ID. The Public ID is visible on the Participants tab so you can use this ID to delete participant data, for example if they choose to withdraw. It may also be an external ID, for example if participants come from Prolific this will show their Prolific ID (but you won't be able to see their actual data alongside this). The Private ID is randomly generated by Gorilla and stored separately from the Public ID by default. When you download your data, it's the Private ID that you'll see in the dataset and not the Public ID, which keeps the data anonymous. However, if for any reason you need to match the participant's identity to the data you can choose to connect the two pieces of information yourself by unblinding the data, but this has to be deliberately done by the researcher. The key distinction is that the Public ID enables you to keep track of the participant, but not their data, and the Private ID allows you to keep track of their data but not the participant. If you want to keep track of the participant and their data - you can then choose to unblind the data when downloading the file.
For the avoidance of doubt, IDs from 3rd party recruitment services (e.g. Prolific) are anonymous; we cannot link such an ID and the associated participant data back to an individual. Unless you explicitly collect identifying data (e.g. names or email addresses), your data is most likely anonymous.
By default, data for each participant only becomes accessible when the participant completes an experiment, so if a participant withdraws from an experiment partway through you will not have access to their data. However, you can choose to manually include a participant who is partway through an experiment, which will give you access to their data. You can also choose to manually delete the data for any or all participants at any time.
When getting consent from participants it may be prudent to get explicit consent for using Gorilla and our sub-processors. We suggest the following text:
How will my data be processed?
By taking part in this study you consent to the use of Gorilla and their subprocessors receiving your data. The Gorilla servers are located in the EU, with some ancillary services (emailing, error handling) provided by suppliers in the USA.
In order to have informed consent, you may want to provide more detail, such as:
or
or
HIPAA compliance is a critical consideration when conducting any research involving protected health information (PHI), even in anonymous online studies. Here are some key considerations for maintaining HIPAA compliance in such studies:
By following these guidelines, researchers can conduct anonymous online research studies while still ensuring compliance with HIPAA regulations and protecting the privacy and security of participants' health information.
Technical attrition due to any element between the participant's device and our servers is a reality of internet research, and we want to give you the information you need to make an informed decision.
The impact of technical attrition on your experiment will depend on your recruitment method and your target participants.
On our side – as long as you haven’t included participants at the start node – no Gorilla fees would be due. If you are paying participants through a participant recruitment service, you may need to check their policy. Microsoft Azure guarantees that our servers will be working 99.95% of the time, and generally performs far above this threshold.
Gorilla is built to support the existing BPS (The British Psychological Society) and NIHR (National Institute for Health Research) standards which have strict codes of practice to adhere to, in addition to the legislative requirements of the GDPR and DPA2018.
To fulfil our Art 28 legal requirements as a Data Processor, we offer a Data Processing Agreement to our customers.
Data controllers accept our list of suppliers as part of our terms and conditions. If and when we engage additional sub-processors, the Data Controller is informed.
The Data Controller shall be entitled to object to any such change, provided that the Data Processsor shall not be liable to the Data Controller for any failure to provide any element of Gorilla as a result of such objection.
2021 Brexit Update:
The EU has granted temporary ‘adequacy’ to the UK in relation to its personal data regime until at least 30 April (and potentially 30 June) in order to ensure that personal data can continue to travel from the EU to the UK and vice-versa as it did prior to Brexit.
In parallel to this, we have put in place arrangements to apply if the UK is not deemed ‘adequate’ and is treated as a third country by the EU. Those arrangements comprise the appointment of an EU representative and making available a mechanism pursuant to which you can enter into the EU Standard Contractual Clauses with us.
As a result and regardless of the outcome of the current EU/UK negotiations, EU institutions are able to continue to do business with us in a GDPR-compliant way.
With regard to the personal data processed in the Gorilla System, we are a Data Processor and the customer is the Data Controller. S10 of our Terms and Conditions clarifies this.
For data where the customer is the Data Controller and we are the Data Processor, we use a small subset of our suppliers. We only use services from these suppliers which are limited in scope and strictly necessary to provide our services.
2020 Update
Following the judgment in the Schrems II case issued by the European Court of Justice we have been following the advice and guidance of the ICO and EDPB so that we can implement recommendations swiftly. This is the current advice from the Information Commissioner's Office.
The suppliers this applies to are:
Microsoft Azure
Participant Data collected using Gorilla is anonymous by default. The only exceptions to this are (1) when using email based recruitment policies as Gorilla requires the participants email address to send them emails, (2) experiments in which the researcher elects to use personally identifying participant IDs and (3) the researcher collects personally identifying data as part of their study. In all cases, the participant would have given their consent.
For the avoidance of doubt, IDs from 3rd party recruitment services (e.g. Prolific) are anonymous; we cannot link such an ID and the associated participant data back to an individual.
Rollbar
We use Rollbar for error reporting. In the event that something unexpected happens, we capture that event data and send it to Rollbar so that we can investigate. The error data that is sent to Rollbar depends on the nature of the error. Identifying data will only be sent to Rollbar if necessary to diagnose the error.
Sendgrid
We use Sendgrid for email delivery. This is used to send transactional email to researchers (account setup, password recovery) and also to send transactional emails to participants to enable them to take part in studies. Emails will only be sent to participants when researchers use email-based recruitment policies, or if a participant enters their email address to receive reminder emails as part of a longitudinal study. In both cases, the participant will have supplied their email address to the researcher and consented to take part in the experiment.
PostMark
We use PostMark for email delivery. This is used to send transactional email to researchers (account setup, password recovery) and also to send transactional emails to participants to enable them to take part in studies. Emails will only be sent to participants when researchers use email-based recruitment policies, or if a participant enters their email address to receive reminder emails as part of a longitudinal study. In both cases, the participant will have supplied their email address to the researcher and consented to take part in the experiment.
We have appointed Prighter as our EU Representative. You can contact them by submitting a request, or via their physical address:
9 Clare Street
Dublin 2 D02 HH30
Ireland
Please add the following subject to all correspondence: ID-14967537625
What happens to the data in a user’s account if they close their account?
How can a university keep access to data that they paid for?
Follow the link to view a List of Suppliers.
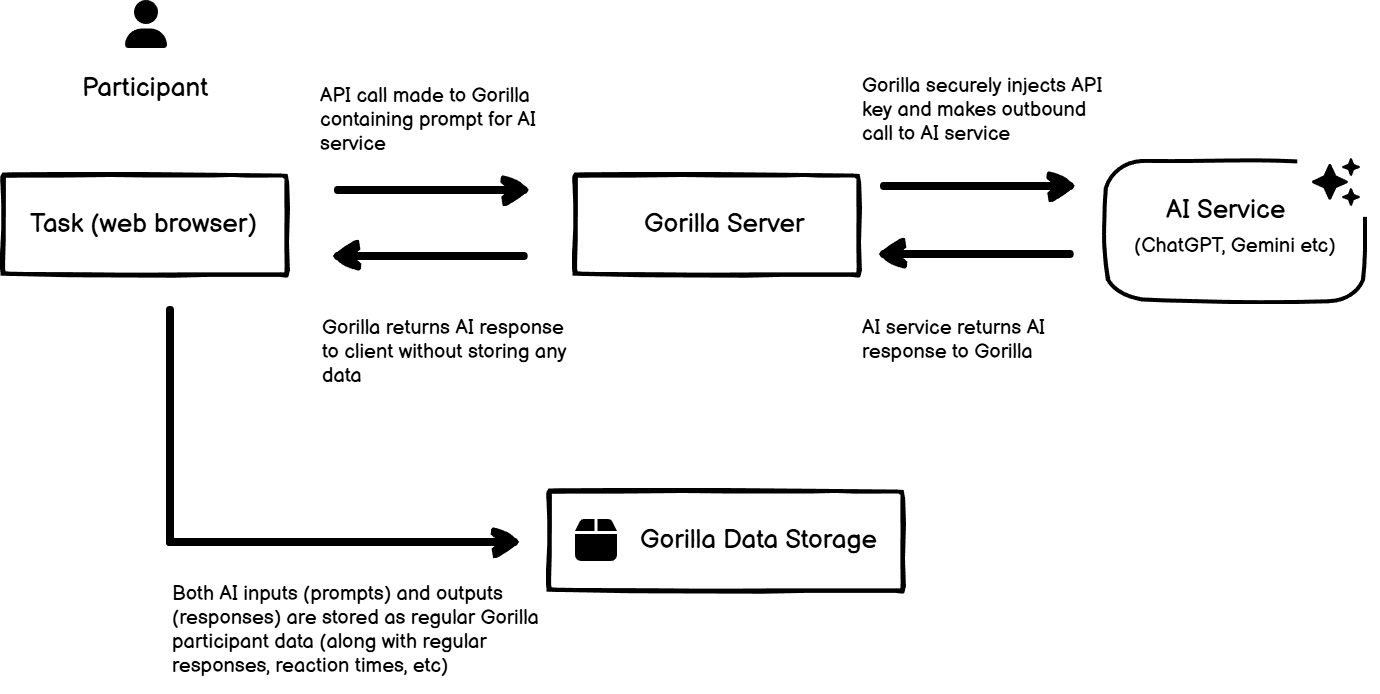
We have added the ability for researchers to integrate AI into their tasks. AI is only used in experiments when the researcher has explicitly added and configured it - Gorilla never sends any participant data to AI services internally. In order to secure the the researcher's API key, all calls to the AI service pass through the Gorilla server. The prompts and responses are then stored in the same way as regular Gorilla participant data (along with regular responses, reaction times, and so on). Gorilla doesn’t store any extra data along the way - everything that Gorilla has stored is in the data output. As per our Terms and Conditions, researchers are responsible for ensuring the legality, accuracy and compliance of any AI they choose to use.
As a data flow diagram:
In addition to functional cookies (e.g. sessions and authentication), we use cookies for Google Analytics for analytics and Facebook for marketing attribution. These are only set if the user permits them first, using the banner that appears at the bottom of the screen when they first access the site:
These cookies are only set on the researcher side of Gorilla - we don't use marketing cookies on the participant-facing research.sc domain.
We hold Cyber Essentials Plus certification: Certificate of Assurance - a6d4ef89-cb2b-4c47-80a6-863ee4d8c883. The registration can be viewed by entering ‘Cauldron Science Ltd’ into the search area.
Gorilla is a secure, cloud-based SaaS platform used for behavioural and cognitive research. The platform is designed to meet the security, privacy, and compliance requirements of universities and research institutions, with controls aligned to recognised industry standards.
Gorilla holds a Cyber Essentials Plus Certificate of Assurance, demonstrating independently verified controls against common cyber threats. Our certificate number is a6d4ef89-cb2b-4c47-80a6-863ee4d8c883.
Gorilla is fully GDPR compliant and operates as the Data Processor. Researchers and their institutions remain the Data Controllers.
Gorilla is hosted entirely on Microsoft Azure, which is certified to:
Azure’s certifications cover:
All traffic to and from Gorilla is encrypted using TLS/SSL with a minimum TLS version of 1.2.
All databases and storage systems are encrypted using industry-standard cryptography, provided by Azure.
Gorilla supports:
Institutions may require MFA for all users on their subscription.
Gorilla undergoes annual independent penetration testing. The latest test identified no high-severity vulnerabilities. A summary report is available to universities on request.
Researchers own all User Content and all Research Data collected using Gorilla.
Researchers can delete:
Deletion behaviour:
Backups are handled by Microsoft Azure’s enterprise-grade backup systems, protected under ISO27001-certified controls.
Gorilla follows a secure SDLC aligned with modern development practices:
All participant and research data is stored in Microsoft Azure data centres certified under ISO27001 and SOC standards.
Azure provides:
Universities may verify Azure’s certifications directly with Microsoft.
Gorilla provides a secure, GDPR-compliant research platform with technical and organisational measures aligned to recognised international standards. Hosting on Microsoft Azure ensures enterprise-level physical, logical, and operational protections, while Gorilla’s data-handling practices support the privacy, security, and governance requirements of universities, ethics boards, and infosec teams.
To request access to our full HECVAT (Higher Education Community Vendor Assessment Toolkit), email procurement@gorilla.sc.
At Gorilla we understand the importance of ensuring our product is accessible to all users. We strive to have an inclusive offering through the following approaches:
Here is our current roadmap:
Not yet scheduled in detail. We are currently working with our users and scientific advisors to design the right set of accessibility features to support their research, while ensuring that important methodological parameters are preserved.
For more information about this, please email info@gorilla.sc.
We can provide a completed VPAT (Voluntary Product Accessibility Template) form for our webpages and the Gorilla application.
The VPAT is a free template that translates accessibility requirements and standards (e.g., in Section 508 and other legal frameworks) into actionable testing criteria for products and services. Users should test their products and services against each section of the VPAT and use the template to document results. Once completed, the VPAT® with documented testing results is referred to as an Accessibility Conformance Report (ACR) that details the accessible features of the tested product or service.
The Accessibility Conformance Report (ACR), based on a completed ITI VPAT®, is the leading global reporting format for assisting buyers and sellers in identifying information and communications technology (ICT) products and services with accessibility features. The VPAT includes the leading ICT accessibility standards: Section 508 (U.S.), EN 301 549 (EU), and W3C/WAI WCAG.
To request a completed VPAT, contact info@gorilla.sc.
We incorporate accessibility features as part of our development process, and continue to improve our existing tools as we develop them. If you have any problems accessing our site, please get in touch with our support team via our support contact form.